The “High Level” Overview of Tenable & Vicarius
So, if you are reading this I am guessing that you are thinking about implementing (or updating) a vulnerability management (VM) programme within your organisation.
If that is the case then it is worth digging into why you are doing this, and explain the steps that you’ll need to go through.
If you need to understand more about your security posture use our Cyber Security Maturity Assessment Model to assess your current attack surface, existing plans and solutions.
Most organisations implement a VM programme because they want to improve their security posture. An objective delivered by following this “high level” 3 step model:
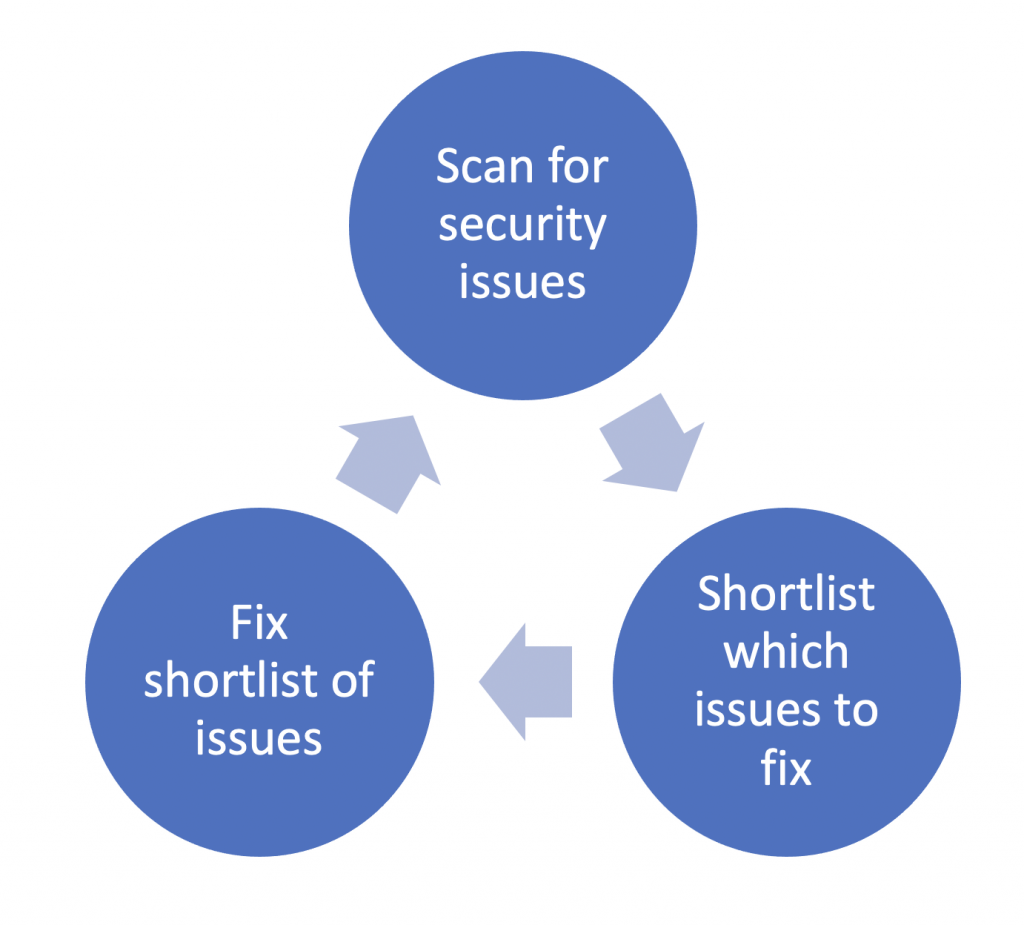
- Work out what security issues and vulnerabilities are present
- Build a short-list of priorities that you will fix
- Fix everything on the short-list
As companies grow and need to scale their security efforts, we recommend shifting to our 8 step model – which covers best practice for effective vulnerability lifecycle management. You can read more about those steps and how to apply them in our best practices blog here.
From the above 3 step model, ultimately it is step 3 that delivers on the objective of “improving security” posture; steps 1 and 2 are the means to that end.
I don’t want to down-play steps 1 and 2, they are still very important, but having the best scanning tool or best short-list in the world won’t improve security.
Before moving on to talk about steps 1 and 3 in more detail, we should explain our reasoning about step 2; building a short-list.
There is a comprehensive range of vulnerability products devoted to prioritising security fixes; again this is discussed in more detail within the 8 step model. For smaller companies, just saying “Let’s fix anything with a severity score of 8 or above …” is usually good enough. Fixing everything would be great; but isn’t realistic.
You can also download for free our 8 step model in our e-book Vulnerability Lifecycle Management.
Why is scanning everything unrealistic?
If you scan a typical server you will get around 100 issues with scores from 1 up to 10; hopefully lots of the former and few of the latter.
Some items don’t have patches available. The Samsung Smart TV in our office is one of these. It is running the latest TV OS from Samsung, and the issues are very low scores so we ignore it.
Upgrading some things will break others; Java is a common example here. So you just have to run old software with issues.
Getting a list of issues
The market for tools to identify and collate a list (Vulnerability Scanners) is mature with lots of options available including Tenable and Vicarius.
Scanners don’t all work in the same way, and when presented with the same environment, different tools will give a variety of results.
Most scanner products will do the basic job and identify machines that are susceptible to things like Eternal Blue (the vulnerability that underlies WannaCry), but as you move through a larger list of vulnerabilities the products differentiate in their performance.
Note that there were over 20,000 CVE (security vulnerabilities) publicly reported in 2020 and there is not one tool will discover them all.
How the scans are performed
It is worth considering how the products work to understand the differences. Some products just look at the outside of the machine.
If that scanner wanted to test SMB for example, it would send a connection request to the target machine. That machine would then answer with a response including version information, and the scanner would then look this response and information up in a database to get the list of vulnerabilities associated with that implementation of SMB.
For some protocols, version information is not given, so the scanner needs to start the conversation, and watch how the response comes back, then infer from there. As you can imagine this can have issues around accuracy.
With some scanners you can do what is called an “authenticated scan”, this is where you provide usernames and passwords. The scanner can then log in and look at the version information on DLLs and the like.
This is a much more accurate way of identifying vulnerabilities and compiling a list. It comes with the down-side that you are allowing additional code to run on that target machine while the scan runs.
A continuation of the authenticated scan, is the agent. This is where you permanently install an agent on the target machine that watches over it all the time.
This can be good for occasionally attached machines (for example a salesperson’s lap-top when he is not in lock-down), where the scan happens at one time, and the information is reported back to the central console when it is next on the internet (at a completely different time).
So you end up with a trade off. The best scans are done by agents, but they have the biggest impact on the business, because you have software installed and running on the machine, all at the same time.
As you step back to authenticated scans, and then non-authenticated scans, they get easier to deploy but less accurate.
Some vendors (Tenable for example) offer all 3 ways of performing a scan (external, authenticated and agent). Other vendors may offer just one or two ways of performing the scan.
How detailed does the scan need to be?
The industry defines security issues as a CVEs (Common Vulnerability and Exposures).
They also give each CVE a severity score to indicate how bad it is, called the CVSS (Common Vulnerability Scoring System). The CVSS goes from 0 (don’t worry) to 10 (start to panic). All of the scanners will find a CVSS score 9 or above with a core Windows components.
Things start to get more interesting and varied if you want to scan a machine running an operating system other than Windows. Linux is pretty well covered, but Mac OS is less so, then you end up with things like Cisco IOS, Samsung and so on. The further you move from Windows the less tools cover it.
The same is true for applications. Microsoft Office, Microsoft SQL Server are all covered very well, Adobe Photo Shop is also covered but not as well. By the time you get to WinZIP or some obscure package on Linux then the coverage will be much less.
Tenable list their 150,000+ plugins here https://www.tenable.com/plugins so that you can see what they check for.
If you are an enterprise organisation then you’ll probably have a large mix of technologies that you want to look for. If you have a business that is more in the small or medium sized range, then a scanner that just looks at Windows and Linux will probably cover your needs.
So ask yourself, how good does the coverage list need to be? It depends on your organisation as to which type, or types of scanner are best when choosing between Tenable and Vicarius.
Building a short-list
This is a long and complex subject that is covered in detail in our 8 step model so I will not spend more time on it here.
Fixing things on the short-list
This is the really time consuming bit.
Whilst you can initiate a vulnerability scan on a Friday night as you go home, and receive your report Monday morning, the actual application of patches is the slow part.
Roughly speaking a patch has the following sub-steps:
- Find the patch on the Internet (the scanners often help with this)
- Apply the patch
- Potentially re-start the system
- Verify that the patch has been applied
- Update the short-list
There is also the potential issue that a patch may not be available for a particular CVE. Sometimes this is because the patch is under development and is not available yet, and other times because the vendor has stopped patching that platform version (think Flash Player which was retired on 31st December 2020).
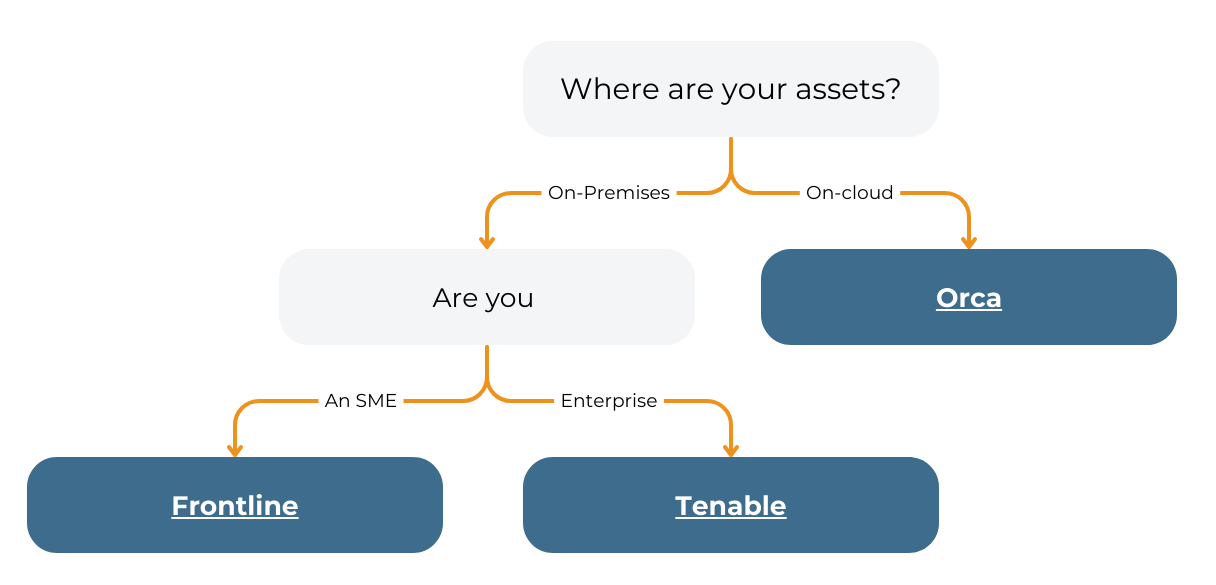
Which is the right tool for you Vicarius or Tenable?
We sell two different scanning technologies because we feel that they address different customer needs.
In summary we would say that larger customers should probably go for Tenable, smaller organisations for Vicarius and medium customers have the option to look at both.
The biggest difference between the two is the inclusion of prioritisation and patch management with Vicarius.
At the top of this post I said that there were 3 steps within a VM programme:
- Work out what security issues and vulnerabilities are present
- Build a short-list of priorities that you will fix
- Fix everything on the short-list.
Vicarius will help with all 3 of these, Tenable just does point 1. Tenable does a better job of point 1 i.e. the scan, but it stops there.
The reason that we suggest smaller companies use Vicarius is because it is often the same person doing all 3 steps. If not the same person, then a colleague probably in the same team.
In a larger organisations the roles are often split up with security focusing on steps 1 and 2, then the mainstream IT team focusing on step 3.
The following table tries to compare the products in an even handed way, which is very hard because these tables are usually used to lead people down a specific path, and that is not our objective; we want to find the right solution for your needs.
| Feature | Tenable | Vicarius |
|---|---|---|
| Platform Coverage | Very broad | Windows, Linux and common applications |
| Depth of CVE scan | Probably the best in the industry | Everything that is important |
| Patching | No real functionality alone, needs other products to help | Included plus proprietary technology for patching things where a vendor patch is unavailable / too hard to install |
Target Customers
For SME organisations up to say 1,000 scanned machines we would generally suggest Vicarius as the best tool.
For organisations beyond say 2,000 scanned machines, we would suggest that the Tenable tools offer the better fit. With this size of organisation they generally change their internal structure and responsibilities and this triggers the demand to change the tool they are using.
Which product is best Tenable or Vicarius?
The Tenable tools do the best job of infrastructure vulnerability detection that we have seen. They also handle very large numbers of assets very well.
Vicarius brings together scanning, prioritization and patching on a single platform. If you are responsible for all of these items then Vicarius is usually the best solution.
Making real-world decisions
A vulnerability management process is not really about vulnerability scanning, it is about patching.
It is the patching that improves the company’s security posture, it is the patching that is the “hard” bit to achieve.
If the company cannot patch fast enough, then having a better scanner just means you have a longer list of things that need to be patched.
When companies hit a certain size they split scanning and patching teams, and often have different management structures to deal with these activities.
If the teams have different management then having separate tools and an SLA between them makes sense.
In this situation we would recommend the Tenable tools (and if big enough Brinqa to manage the SLA other other things).
If the teams have the same management, then an integrated tool like Vicarius makes sense.
What is your area of responsibility? Are you just focusing on getting lists of issues, or are you interested in generally improving security?
If your role is more audit / compliance focused then the Tenable products make far more sense. They do a better detection job.
If you care more about security as a whole, then Vicarius is the better choice. As an organisation if you have all the CVSS score 5-10 items patched, but have not found some level 1 items, then you are in a great place.
Next steps
If you want to learn more about Vicarius or Tenable visit our case study page or ask for quote.
Read more about risk based vulnerability management and our Brinqa case studies, or check out the Brinqa page or contact S4 Applications to request a demo.