Core Impact
Core Impact, Fortra’s powerful penetration testing software solution provides insight into potential vulnerabilities, and allows users to run routine automated tests, as well as select from a library of exploits.
The Choice of the Penetration Testing Community
Find your Organisation's Weak Points.
Fortra’s Core Impact is a powerful penetration testing platform designed to enable security teams to conduct advanced tests with ease. With guided automation and certified exploits, you can safely test your environment using the same techniques as today’s adversaries.
The choice of the Penetration Testing Community, Core Impact is an analytics-driven solution for assessing and testing security vulnerabilities throughout your organisation.

Core Impact Optimises the Use of your Resources.
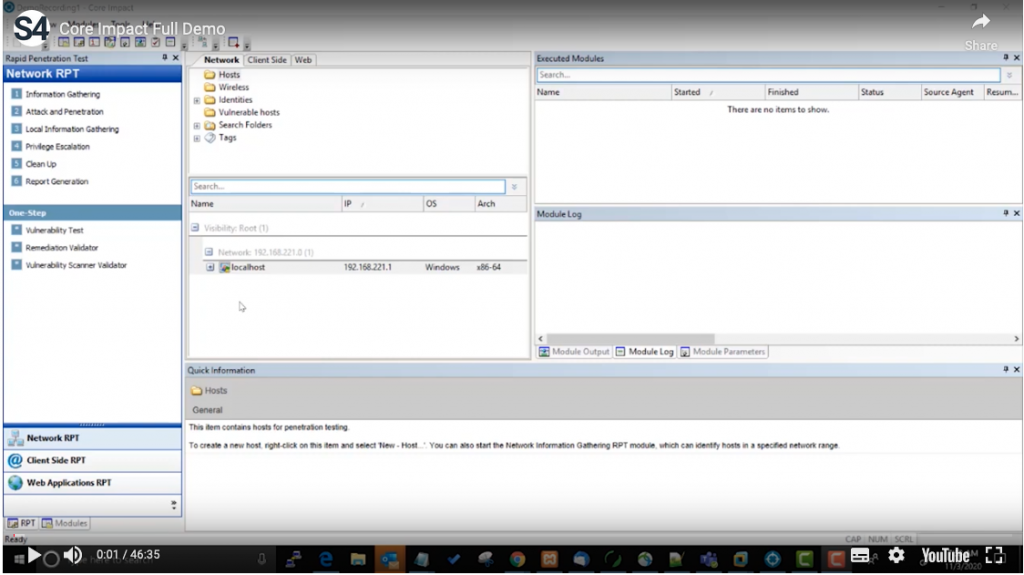
With Core Impact your IT security team can automate manual processes with Rapid Penetration Tests (RPTs) using consistent data, prioritisation methods and reporting. simplifying processes, maximizing efficiency, and enabling pen testers to focus on more complex issues.
Reduce remediation time, minimise risks, secure critical assets and maintain continuous compliance. Core Impact allows you to quickly re-test exploited systems to verify that remediation measures or compensating controls are effective and working.
Gather Information, Exploit Systems, & Generate Reports, All In One Place.
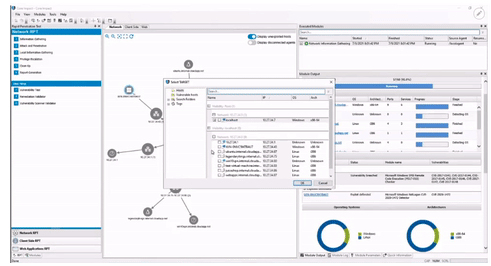
Using an up-to-date library of commercial-grade exploits, developed and tested by Fortra’s own cybersecurity experts, Core Impact reveals how chains of exploitable vulnerabilities open paths to your organisation’s mission-critical systems and assets.
Every phase of the penetration test process can be executed and managed from a single console with an intuitive dashboard.
Instead of switching back and forth between tools, additional solutions can also be integrated or incorporated to further expand your testing programme, such as Cobalt Strike, OST.
Validating Vulnerabilities Surfaced Through Scanners.
Why Core Impact?
Core Impact’s flexible pricing model ensures your business can leverage market-leading technologies to suit your specific use case and budget.
- Intuitive automation for deploying advanced level tests
- Extensive and reliable library of certified exploits
- Multi-vector testing capabilities
- Ransomware simulation
- Teaming capabilities in a collaborative workspace
- Tailored reporting to build remediation plans
- Powerful integrations with other pen testing tools and more than 20 third-party vulnerability scanners
- Robust safety features, including fully encrypted, self-destructing agent
- Enable programmable self-destruct capabilities for agents, so no agent is left behind after testing to drain resources or be used as a potential backdoor for attackers.
Next Steps - Get Started
As a Fortra partner, S4 Applications works with clients to help them understand their attack surface, priorities, and goals. We develop a roadmap to deploy the right solution for your needs. Read more about our Fortra case studies, learn more about Fortra or contact S4 Applications.
Related Resources
What are Cobalt Strike doing to evade EDR?
Cobalt Strike and Endpoint Detection & Response (EDR) solutions.
Ransomware Simulation by Core Impact
Core Impact’s new ransomware simulation feature is a great way to prevent malware from stealing your data or locking you out of your computer.