The Industry's Best Technology Vendors
Transform your Vulnerability Management with Brinqa.
Vendor Features
- Automates vulnerability management processes from scan, to risk prioritisation to ticket management
- Automates risk acceptance process and mitigations
- Provides dashboard / reporting
- Out of the box “data warehouse” for your cyber security data
- Over 100+ connectors to industry leading technologies
Benefits
- Visibility across all vulnerability risk in one place
- Reports on issues based on risk severity
- Tickets only closed when verified by scanner
- Focuses time only on the exceptions not running processes
- Helps enforce SLAs between departments
- Verifies remediation
Improve Compliance And Accountability In Your Organisation.
Vendor Features
- Fortra Vulnerability Manager, Outflank Security Tooling, Core Impact, and Cobalt Strike
- Threat prioritisation for enhanced efficiency
- Automated detection and prioritisation
- Replicate attacks for improved resilience
- Real-time status views and customisable compliance reporting
Benefits
- Save time – detect infections and remediate faster
- Enhance and upgrade your pen testing capabilities
- Cut remediation time, minimise risks, secure critical assets
- Fortra’s cybersecurity and automation offerings give your organisation the tools you need to meet the challenges of today’s threat landscape.
- Vulnerability scans and reports pinpoint which vulnerabilities are present.

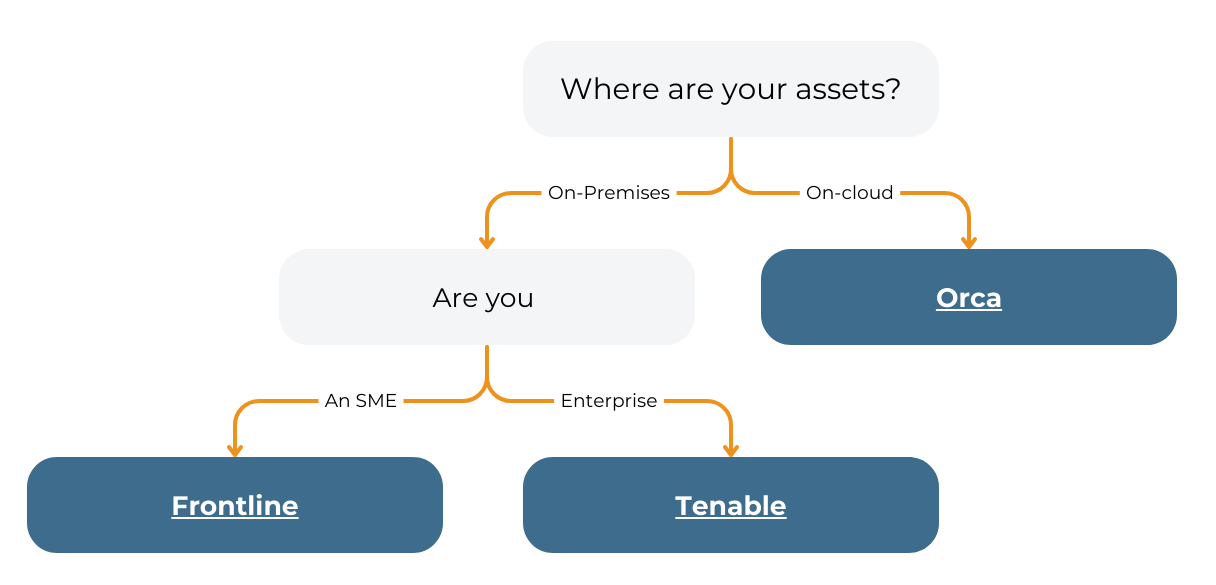
Orca Security Provides Instant-on Security and Compliance
Orca brings together core cloud security capabilities, including
vulnerability management, compliance and more in a single, purpose-built solution for AWS, Azure, GCP, and Docker / Kubernetes.
At Orca Security, their innovative Cloud Security Platform enables companies to scale in the cloud with confidence and close the loop on alerts faster than ever before. The Orca Platform is the first cloud-native application protection platform (CNAPP). Automatically links cloud risk detections in production with the development pipeline.

A Web Application Scanner that Scales.
Invicti is a scalable, multi-user, web application security solution with built-in workflow and reporting tools.
Obtain a comprehensive view of your web security posture that can be integrated within your SDLC. Invicti doesn’t require you to have extensive IT security knowledge, a market leader that combines cutting-edge technology with an excellent user interface.
The application explains the errors causing the vulnerabilities so your security team can easily eliminate them.

Translating Vulnerability Data into Business Insights
Tenable adheres to the principle that there is no one-size-fits-all approach to cybersecurity. It’s range of products improve resilience, detection, speed, efficiency and predictive prioritisation for an enterprise organisation.
The Tenable platform can holistically assess, manage and measure cyber risk across the modern attack surface and communicate cyber risk in business terms to make better strategic decisions.
- Tenable Nessus Pro, Tenable Nessus Expert, Tenable Security Center and Tenable Vulnerability Management
- Active and passive assessment of systems, networks and applications
- Continuous monitoring of users, applications and infrastructure
- Real time alerts and notifications
- Intelligent vulnerability prioritisation
- Broad vulnerability coverage
- Assessment and dynamic asset tracking
- Intuitive dashboard visualisations, automated workflows, and flexible API
- 70K CVEs – the most in the industry. Nessus scans more technologies and uncovers more vulnerabilities than competing solutions.