What is Nessus?
Nessus, developed by Tenable, is a platform that scans devices, applications, operating systems, cloud services, and other network resources for security vulnerabilities.
Originally launched as an open-source tool in 1998 called “The Nessus Project“, Nessus transitioned to a commercial product with its enterprise edition in 2005. Today, Nessus includes several products that automate point-in-time vulnerability assessments of a network’s attack surface. The goal is to help enterprise IT teams stay ahead of cyber attackers by proactively identifying and fixing vulnerabilities as they are discovered, rather than waiting until after they are exploited.
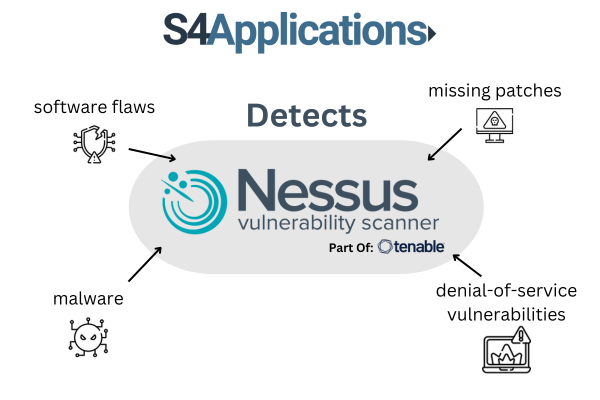
Nessus detects software flaws, missing patches, malware, denial-of-service vulnerabilities, default passwords, and misconfiguration errors, among other issues. When Nessus identifies vulnerabilities, it alerts IT teams, who can then investigate and decide on any necessary actions.
What is a denial-of-service (DoS) vulnerability?
A denial-of-service (DoS) vulnerability is a weakness in a computer system, network, or application that can be exploited to make the service unavailable to its intended users.
Here’s a simple analogy: Imagine a popular coffee shop with limited seating. Normally, customers come and go, enjoying their coffee without any issues. However, if a large group of people, who don’t intend to buy anything, occupy all the seats and refuse to leave, paying customers can’t find a place to sit and enjoy their coffee. In this scenario, the coffee shop is experiencing a “denial-of-service” because legitimate customers are being denied the service they came for.
In the context of cybersecurity, a DoS attack typically involves overwhelming a target system with excessive requests or exploiting certain vulnerabilities to crash or significantly slow down the system, making it unusable for legitimate users. There are different types of DoS attacks, including:
- Flood Attacks: Sending a massive amount of traffic to overwhelm the system.
- Crash Attacks: Exploiting bugs or vulnerabilities that cause the system to crash.
- Resource Exhaustion Attacks: Consuming the target’s resources (like CPU, memory, or disk space) to the point where it can’t function properly.
These attacks can cause significant downtime, financial loss, and reputational damage to organizations. Identifying and mitigating DoS vulnerabilities is crucial to maintaining the availability and reliability of online services.
What does Nessus do?
Nessus is renowned for its extensive plugin database. These plugins are dynamically and automatically integrated into the tool, enhancing its scan performance and minimising the time needed to assess, research, and remediate vulnerabilities. Additionally, plugins can be customised to create specific checks tailored to an organisation’s application ecosystem.
Nessus includes a feature called Predictive Prioritisation, which uses algorithms to rank vulnerabilities by their severity, helping IT teams identify the most urgent threats. Each vulnerability is given a Vulnerability Priority Rating (VPR) on a scale from 0 to 10, with 10 indicating the highest risk, categorising them as critical, high, medium, or low. IT teams can also utilise pre-built policies and templates to efficiently detect vulnerabilities and assess the threat landscape.
Why Nessus for cyber vulnerability management?
- Number 1 for Accuracy: Nessus boasts the industry’s lowest false positive rate, achieving six-sigma accuracy.
- Number 1 for Coverage: Nessus offers the deepest and broadest vulnerability coverage in the industry.
- Number 1 for Adoption: Nessus is trusted by tens of thousands of organisations and has been downloaded 2 million times worldwide.
Who is Nessus for?
Nessus is an essential tool for a variety of cybersecurity professionals and organizations. It serves consultants and penetration testers who require robust capabilities for identifying vulnerabilities and assessing security risks. Deployed on-premises, Nessus utilizes active scanning techniques to gather comprehensive data about network and application vulnerabilities.
For consultants, Nessus facilitates in-depth security assessments and audits, providing detailed insights into potential weaknesses that could be exploited by attackers. Penetration testers rely on its advanced scanning features to simulate real-world attacks, helping organizations fortify their defenses against malicious intrusions.
Furthermore, Nessus is indispensable for periodic vulnerability assessments, ensuring that IT teams stay proactive in identifying and mitigating security risks. Its extensive plugin database and predictive prioritization feature assist in prioritizing vulnerabilities based on their severity, enabling efficient allocation of resources for remediation efforts.
Overall, Nessus is tailored for cybersecurity professionals and organisations seeking robust, reliable tools to enhance their security posture and safeguard against emerging threats.
Learn more about Tenable Nessus Professional, the Industry Standard For Vulnerability Assessment and Tenable Nessus Expert built for the modern attack surface.